Thus far, we have wondered whether Harvard sophomore Mark Zuckerberg may have committed a tort when he created Facemash back in ’03. Broadly speaking, whether an act or omission constitutes a civil tort depends on the common law of the place in which the alleged tort occurred. But remember: the United States is a federal system! There are two levels of government in the USA–the States and the feds–and each level has its own laws and operates its own separate legal system. As a result, in addition to local tort law, there are a number of federal laws that could have applied to Facemash. In particular, Facemash may have crossed the following three federal legal lines:
- Copyright infringement under the Copyright Act of 1976.
- Unauthorized access to a protected computer under the Computer Fraud and Abuse Act of 1986 (CFAA).
- Breach of privacy rights under the Family Educational Rights and Privacy Act of 1974 (FERPA).
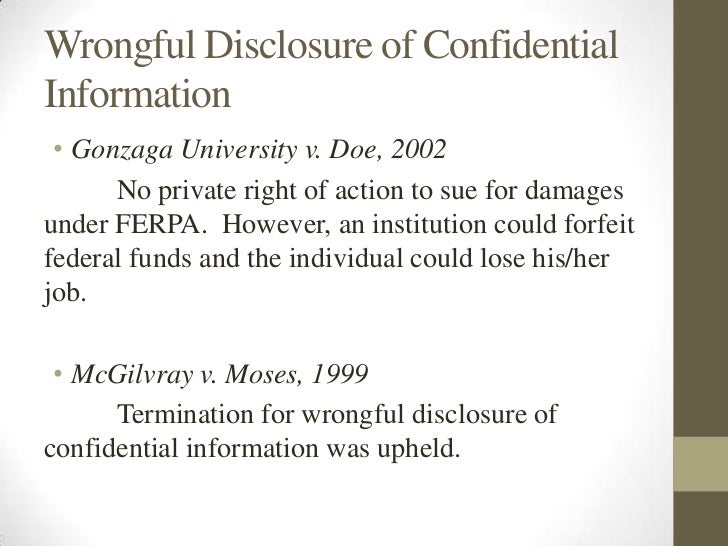
Frankly, we should just ignore FERPA because this toothless federal privacy law is all bark and no bite. In theory, the Secretary of the U.S. Department of Education could have brought a FERPA enforcement action against Harvard (perhaps on the theory that Harvard did not do enough to protect sensitive student information from hackers), but FERPA applies only to “educational records”, so a strong argument can be made that Facemash did not run afoul of FERPA. But even if student I.D. photos are considered “educational records”, the U.S. Supreme Court ruled in Gonzaga University v. Doe, a case decided in 2002, that private parties may not sue for damages under FERPA. (By the way, it’s also worth noting that the feds have never brought an enforcement action under FERPA!)
That still leaves copyright infringement and the CFAA, two federal laws that do allow private causes of action, i.e. private parties may sue for money damages under the Copyright Act and the CFAA if certain conditions are met. In addition, copyright law and the CFAA also establish severe criminal penalties (!) for copyright infringement and for unauthorized access to a protected computer, so we will take a closer look at these two laws in our next two blog posts.
Credit: Elaine Daniels



Drop top. Head boppin’.
“2Chainz”!!! I love that song…