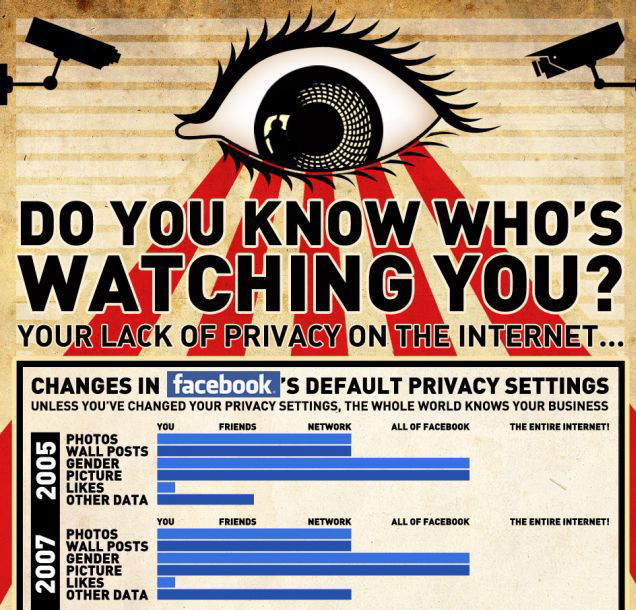
A major source of local (i.e. State) law in the USA is judge-made common law. In fact, major areas of local law–including torts, contracts, and property–are based on well-established common law principles. Here, we will focus on the law of torts. A tort is a wrongful act, such as assault, battery, and trespass, and a tortfeasor is a person who commits a tort. (Note: a tortfeasor could be an LLC or a corporation.) When someone is injured by the commission of a tort, he or she may have a legal right to sue the tortfeasor for money damages under one or more theories of tort liability. So, did Zuckerberg commit a tort when he hacked into Harvard’s computers and launched Facemash?
In our view, at least three or four theories of tort liability could apply to Facemash: (1) conversion, (2) trespass, (3) invasion of privacy, and perhaps (4) intentional infliction of emotional distress. Let’s start with common law conversion, which is a fancy word for theft. There is no doubt that Zuckerberg did not have a legal right to use the student I.D. pictures in Harvard’s computer databases when he created Facemash, so one could argue that the Facemash hack constituted an act of conversion. But there are big two problems with this theory of liability. First, in the case of Facemash, who would have standing to sue under such a theory? That is, since only the owner has legal standing to enforce his property rights, we must ask: who owns the legal rights to the student I.D. pictures that were posted to Facemash? Each individual student or Harvard? But beyond legal standing, the more fundamental problem with this legal theory is that it’s not at all obvious that a “conversion” really occurred in this case. After all, Zuckerberg did not try to prevent anyone else from using the photos; that is, he didn’t really steal or convert those pics; he just made digital copies of them!
What about trespass? For example, the tort of trespass to chattels–what the famed torts scholar William Prosser once called conversion’s “little brother”–occurs when a person interferes with another person’s property rights. Alas, courts are divided whether this tort applies to such online activities as “screen scraping“. Most courts will require the plaintiff (the person who is suing the alleged trespasser) to prove actual damages or monetary losses. In the movie “The Social Network,” Facemash causes Harvard’s computer system to crash, so Harvard might be able to prove damages, but it wasn’t the actual hacking of the student I.D. photos that caused the system to crash; it was Facemash’s popularity among users. That is, Harvard’s system crashed after the network was hacked! Further, does Harvard really want to sue one of its own students? Also, doesn’t the fact that Harvard did not expel Zuckerberg hurt Harvard’s ability to sue for trespass? In any case, besides trespass and conversion, two other common law theories of legal liability could apply to Facemash: invasion of privacy and intentional infliction of emotional distress (“IIED”). Stay tuned; we will consider these two tort theories in our next blog post.